In this section, by defining filters globally, definitions are made so that they are available and selectable in API Gateways.
Filters is the policy that provides security with a Content Control-based defense against API/Web Service attacks. If the filter/filters you have defined are in the header, parameter and message content (body) of the requests from the client, they will be blocked or deleted by Apinizer. Apinizer offers two different options to API developers to block or delete the request.
There are 17 default filters made available on the Apinizer Platform and widely used in the API world:
- ASCII Control Character
- SQL Delete Attack
- SQL Drop Table Attack
- SQL Insert Attack
- SQL Server Shutdown Attack
- SQL Update Attack
- XML Processing Attack
- XPath (Abbreviated Syntax) Insertion Attack
- XPath (Expanded Syntax) Insertion Attack
- ASCII Control Characters Except Line Feed and Carriage Return
- Content Longer Than 1024 Chars
- DOCTYPE DTD Reference
- Java Exception Information Leakage
- JavaScript Injection Attack
- OR Attack
- Printf Format String Insertion Attack
- Server Side Include Insertion Attack
In addition to the above, you can write your own Regular Expressions.
You cannot edit or delete what is added by default by Apinizer.
Creating a New Filter
From the Administration → System Settings → Predefined Values → Filters screen, click the +New button.
The picture below shows the predefined filter creation settings:
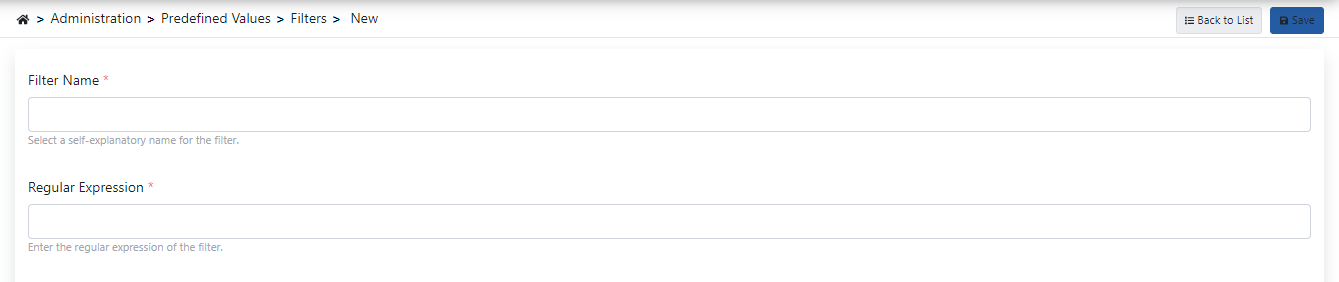
The fields used for the filter creation configuration are shown in the table below.
Field | Description |
|---|
| Filter Name | This is the field where the name of the filter definition is entered. |
| Regıular Expression | This is the field where the regular expression is entered. |