Rate Limit Control List (RLCL)
Why Do We Need This?
APIs are everywhere in the digital world! Applications talk to each other, systems share data, devices are constantly connecting. This level of open, intense communication inevitably brings certain security risks. Abuse, attacks, service outages—so it's no longer enough to ask only "who can access?" We also need to ask "who can access how much?"
In the dynamic world of API development and management, controlling the flow of incoming requests is essential to maintain system stability, ensure fair usage, and prevent abuse.
That's exactly where we at Apinizer come in:
Our Inspiration: Access Control Lists (ACL)
The "Access Control List" (ACL) concept, used in security for many years, determines who can access certain resources. It is list-based, target-oriented, and contains clear rules. At Apinizer we thought: "Why not use this logic for rate limiting?"
And Rate Limit Control List (RLCL) was born.
ACL vs RLCL: Apinizer's Powerful Dual Solution
Apinizer offers both ACL and RLCL solutions for security and traffic management. The two solutions complement each other to fully protect your APIs:
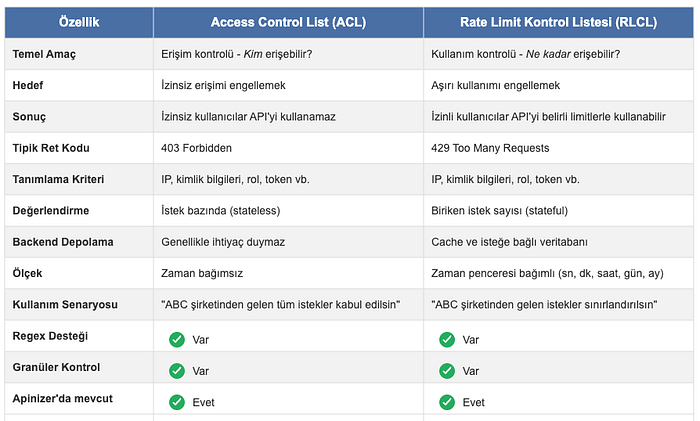
By using these two powerful mechanisms together, you can make your API security complete. First define who can access with ACL, then define the limits of that access with RLCL.
So What Exactly Is RLCL?
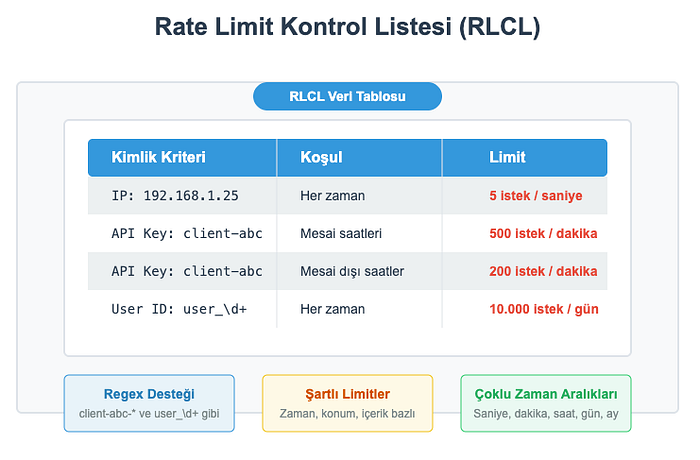
As the name suggests: a system that lets you define rate limit rules in a list-based, targeted way. You no longer have to apply a single limit to every IP, every API key, every user. You can define custom limits such as:
- 5 requests per second for IP
192.168.1.25, - 500 requests per minute for API keys starting with
client-abc-*, - 10,000 requests per day for specific user IDs
You can also use regex-supported or conditional definitions (e.g. different limits during business hours vs. outside). So the era of "one rule for everyone" is over!
How Does RLCL Work in Apinizer?
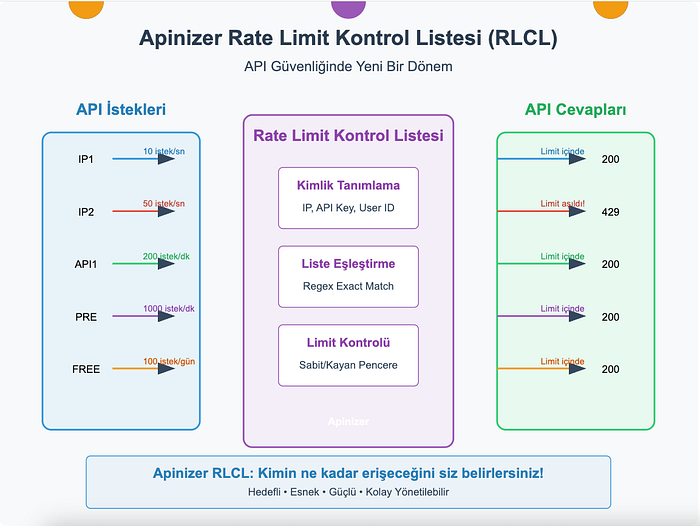
It's not complicated; the steps are clear:
- A request arrives.
- Identity information is extracted from the request (IP, header, user ID, etc.).
- The system checks whether this information is defined in the RLCL (does it match the list or regex?).
- If it matches, the rate limit rule defined specifically for it is applied.
- If it doesn't match, credential validation is performed; if the identity is not defined in the RLCL, the request is rejected and an error response is returned.
- If the limit is exceeded, the request is rejected (usually with a 429 Too Many Requests error).
- Optionally, rate limit status can be added to response headers (
X-RateLimit-*).
Apinizer RLCL Flexibility
Apinizer's Rate Limit Control List solution stands out for its flexibility:
Time Window Options
RLCL supports both Fixed Window (FIXED) and Sliding Window (SLIDING) approaches:
- Fixed Window: Counters are reset at fixed time intervals (e.g. every hour)
- Sliding Window: For any moment, requests in the last X minutes/hours/days are evaluated
This lets you offer solutions suited to different business scenarios.
Dynamic Identity Definition
Apinizer RLCL offers highly flexible options for determining request identity:
- IP address
- API key
- User ID
- Request headers
- Cookie values
- URL parameters
- Request body fields
You can even use combinations of these! For example, you can define special rules for "requests with a certain user ID coming from a certain IP block."
Regex Support
RLCL lets you build very powerful matching rules using Regular Expressions. For example:
- All IP addresses starting with
^192\.168\. - All API keys in the format
api-key-[0-9]+ - Email addresses with a certain domain extension
This way you can reduce management overhead by defining patterns instead of individual values.
Simple, Clear Settings
At Apinizer we keep our usual ease-of-use principle and offer you simple, clear interfaces. We handle the hard part in the background. Without worrying about complex rate limiting mechanisms and algorithms, you can meet all your needs with these straightforward settings:
- Name and Description: For easier management.
- Execution Order: Should it run before or after other policies?
- Time Window Type: Fixed or sliding?
- Allowed Request Count: How many requests can pass?
- Time Interval: You can set it in seconds, minutes, hours, days, or months.
- Identity Variable: IP, API key, or user ID?
- Target Identities: You can define them as a list or with regex.
- Response Headers: Do you want to show rate limit statistics?
Why RLCL? What's the Difference?
Granular control: You get clear answers to who can access how much.
Targeted limiting: A single bad actor cannot lock down your entire API.
Flexibility: Partner, customer, service—whoever it is, you can define different SLAs.
Transparency: You can include remaining limit information in responses.
Manageability: Definitions are simple and readable.
Performance: It runs fast with cache support and doesn't slow down your system.
Real-World Examples
-
Free vs. Premium Users: In your freemium service you can apply "100 requests per day" for free users and "50 requests per second" for premium users. Your API stays both accessible and fair.
-
Geography-Based Protection: You can apply different limits to requests from certain countries or IP blocks. This is especially useful for suspicious traffic sources.
-
DDoS Prevention: You can quickly detect IPs sending sudden high traffic and apply special restrictions. Thus you isolate the problem without affecting your other users.
-
Partner Management: You can define specific API usage limits for each business partner. According to everyone's needs—some can make 1000 requests per minute while others make 10 per hour.
Closing Words
At Apinizer we wanted to bring a fresh approach to API security and management. We turned rate limits from just a number into a targeted, flexible, and powerful control tool. Because we know that in the modern API world, "the same rules for everyone" is no longer enough.
Our Rate Limit Control List solution stands out with its adaptable structure for different needs, easy configuration, and strong performance.
With Apinizer, you decide who accesses how much.